Security Operations with ServiceNow®

SYSUSA
03 Jan , 2019

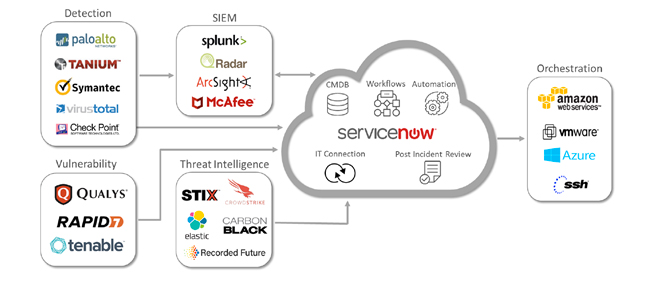
Organizations use many tools in their security operations center providing them with real-time Operational Intelligence. These tools enable organizations to search, monitor, analyze, and visualize data generated from websites, applications, servers, networks, sensors, and mobile devices. Data generated from these tools help organizations identify threats and weaknesses and respond to them in real-time. This data also enables senior management to make informed and fact-based risk management decisions.
The amount of data generated from these tools has the potential to overwhelm the operations team and can reduce their ability to respond to threats in real-time. Integrating intelligence into security operations and automating incident response can help reduce the potential of critical threats going unnoticed or not being addressed promptly. Although, automation and intelligence cannot solve all the problems, it can significantly enhance the organization’s ability to respond to incidents in real-time.
ServiceNow®, named as a Leader in Integrated Risk Management (IRM) in Gartner’s 2018 Magic Quadrant, through continuous monitoring and automation, provides a real‑time view of compliance and risk, improves decision making, and increases performance across the organization and with vendors. ServiceNow® connects business, security, and IT with an integrated risk framework that transforms manual, siloed, and inefficient processes into a unified program built on a single platform.
ServiceNow® collates incident data from a variety of security tools into a structured response engine that uses intelligent workflows, automation, and a deep connection with IT to prioritize and resolve threats based on the impact they pose to your organization.
ServiceNow® Security Incident Response application can track the progress of security incidents from discovery and initial analysis, through containment, eradication, and recovery, and into the final post-incident review, knowledge base article creation, and closure. It enables organizations to gain a comprehensive understanding of incident response procedures performed by analysts and provide insight into the trends and bottlenecks in those procedures with analytic-driven dashboards and reporting.
ServiceNow®, with built-in integrations with third-party cybersecurity solutions and partner-developed integrations from the ServiceNow Store, enable security automation and orchestration for efficient and accurate incident response.
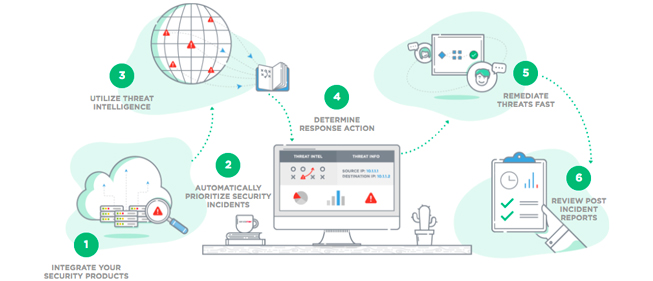
Security incidents can be created manually in ServiceNow® from the form, or automatically by integrating third-party alert monitoring tools, such as Splunk using REST API to generate security incidents automatically. Data is also imported from third-party tools into security alerts.
Events imported from alert monitoring tools are first processed by Event Management and grouped into alerts. These alerts can be used to create security incidents based on customizable alert rules, or manually reviewed to select those alerts to be investigated as a security incident. The alert rule can automatically create security incidents when critical security-related events are received from within ServiceNow® or from third-party monitoring applications. After the security incident has been created, it will be updated as new events are received.
Security Incidents can be assigned to security analysts manually or automatically using the workflows or by using auto-assignment. Auto-assignment allows you to define, based on the needs of your organization, the criteria by which analysts are assigned automatically to security incidents. Auto-assignment can also be customized based on the analyst skills, location, time zone, or group coverage area. When assigning incidents to analysts, they are evaluated based on the weighting property settings and other customized criteria. These configuration settings help auto-assign agents based on optional properties.
ServiceNow’s powerful yet simple cloud platform has the advanced capacity and infrastructure necessary to integrate IT strategy, design, transition, and operation. By centralizing records for all IT processes and supporting the development of unique applications to meet a variety of needs, this platform enables increased efficiency and productivity for all types of business users.
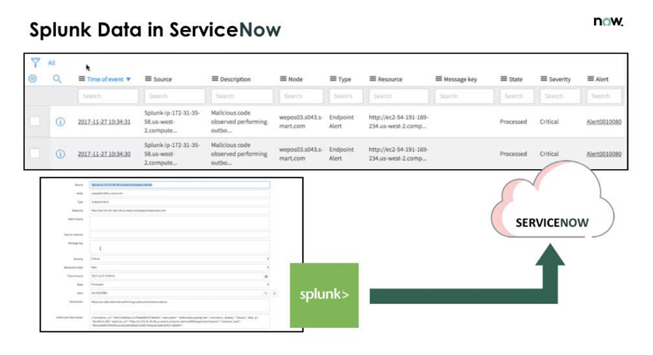
Splunk Integration with ServiceNow
Splunk, out of the box integrations with ServiceNow® Security Operations applications can help organizations to seamlessly create security incidents or events from Splunk events, alerts, and logs. ServiceNow® Security Operations add-on for Splunk also allows Splunk software administrator to collect data from ServiceNow and create incidents and events in ServiceNow. Which are as follows;
- Bi-directional integration between Splunk and ServiceNow
- Trigger Splunk qualified alerts into ServiceNow as incidents or events
- Collect records from incident, problem, change, CMDB or any other ServiceNow table into Splunk for analysis
- Use Splunk agile reporting and advanced analytics to create insights into IT Service Management metrics
The Splunk Add-on for ServiceNow allows a Splunk software administrator to use ServiceNow REST APIs to collect the following types of data.Incident data.
- Event data
- Change data
- User data
- User group data
- Location data
- Configuration management database (CMDB) configuration item (CI) data